Someone Broke Google's SynthID Watermark With Signal Processing. No AI Required.
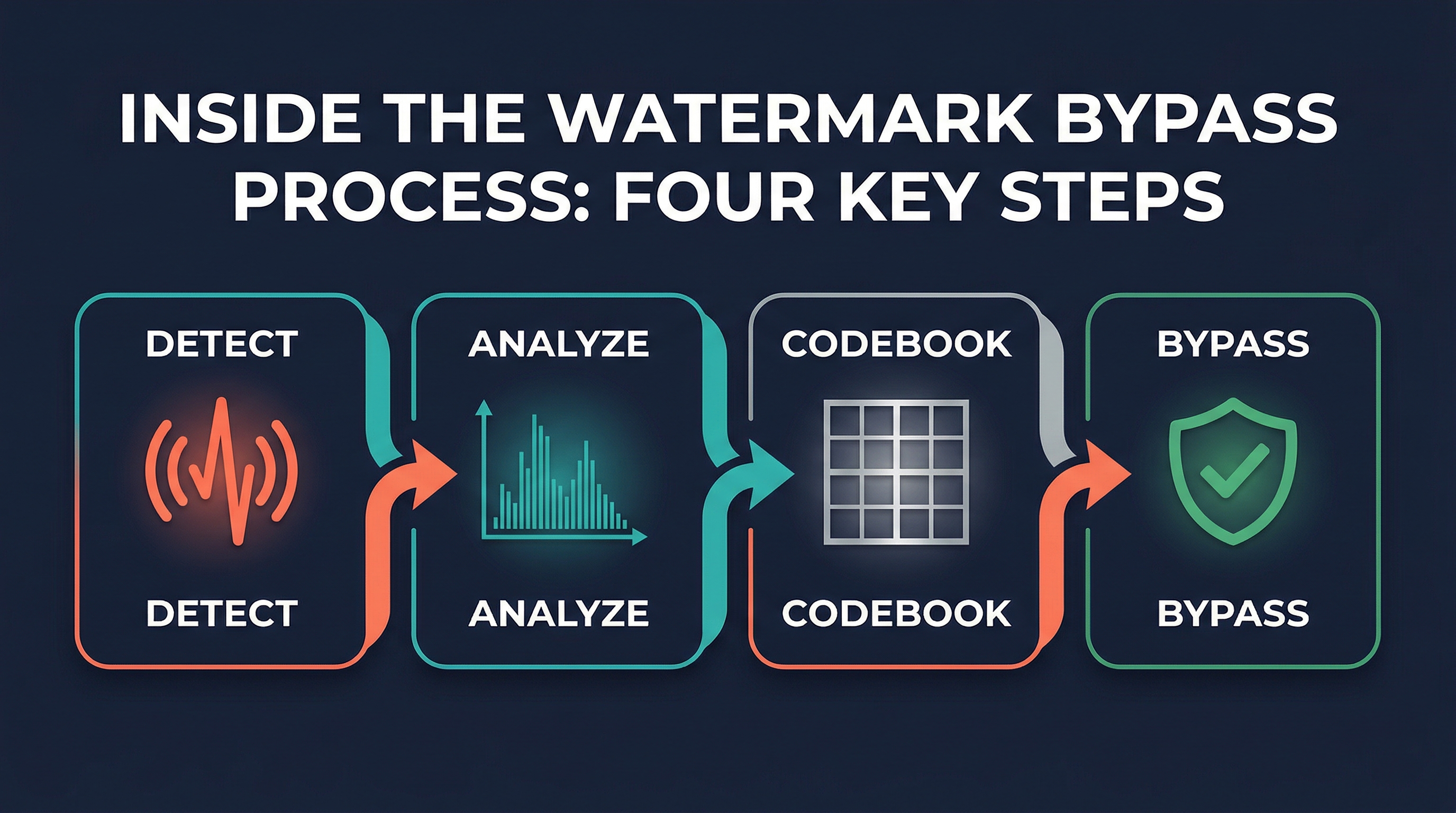
Google's SynthID is supposed to be invisible. It sits in every image Gemini generates and serves as a detection layer for AI-generated content. A developer dropped a reverse-engineering project on GitHub today and HN picked it up fast. The approach is pure signal processing. No model weights. No proprietary APIs. Just spectral analysis of watermarked images and a codebook that undoes what SynthID does.
The results are hard to argue with. Ninety percent detection accuracy achieved. A bypass tool that achieves 75 percent carrier energy drop and 91 percent phase coherence drop. Surgical removal that leaves the image visually intact at 43 plus decibels PSNR.
This is the cat-and-mouse game playing out in public.
How the Watermark Actually Works
The reverse engineering team found something specific and strange. SynthID embeds carrier frequencies at different absolute positions depending on image resolution. At 1024 by 1024, the top carriers sit at frequency bin coordinates 9,9. At 1536 by 2816, they land at completely different bins, 768, 704. The same watermark technology produces entirely different frequency patterns at different sizes.
This matters because it means a codebook built for one resolution cannot remove the watermark from an image at another resolution. The bypass tool that works on a square image fails on a portrait. That was the gap the reverse engineering team exploited.
They built a multi-resolution codebook. The V3 version stores per-resolution profiles and auto-selects the matching one at bypass time. When you give it an image, it figures out which resolution profile applies, loads the right frequency template, and surgically removes the carrier signal from the right bins.
The Detection Results
The detector built from this analysis achieves 90 percent accuracy. That number is not perfect but it is high enough to be useful and low enough to be defeat-able. The bypass tool works against it. Given a watermarked image, the V3 codebook can strip the watermark with results that are visually indistinguishable from the original.
The green color channel carries the strongest watermark signal. That is a specific technical detail worth noting if you are trying to understand why certain bypass approaches work better than others. The watermarking energy is not evenly distributed across channels. It concentrates in green.
There is also a cross-image consistency finding. The phase template is identical across all images from the same Gemini model. This means the watermark is not adapting per image. It is a static modulation applied to every output. Cross-image phase coherence at carrier frequencies exceeds 99.5 percent.
What This Means for AI Content Detection
The methodology is the part that should concern anyone relying on SynthID for content provenance. This was not a model extraction attack or a adversarial attack. It was signal processing. The team analyzed watermarked images, found the frequency patterns, built a codebook, and published the bypass tool.
If you are evaluating AI content detection tools, ask how they perform against frequency-domain attacks. The watermark lives in frequency space. Removing it does too. A system that cannot defend its frequency signature against spectral analysis is relying on an assumption of obscurity that no longer holds.
The arms race between watermarking and watermark removal is real. The removers are winning in public right now. SynthID is Google's flagship invisible watermark and someone broke it with open-source signal processing tools.
Sources: - Reverse SynthID Project (GitHub) - Hacker News Discussion
